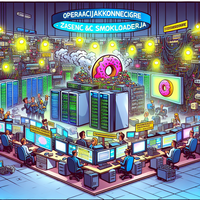
OPERACIJAKONECIGRE – Zasežen C&C strežnik SMOKELOADERja
Oblasti so uspešno zaplenile poveljniški in kontrolni (C&C) strežnik, ki ga je uporabljala zloglasna zlonamerna programska oprema SMOKELOADER. Ta operacija, imenovana “OPERATIONENDGAME”, predstavlja ključni korak pri motenju aktivnosti kibernetskih kriminalcev, ki so strežnik uporabljali za izvajanje zlonamernih aktivnosti po vsem svetu. Podrobnosti o Zaplembi Po poročilih cyberundergroundfeed je bila domena potunulit.org, identificirana kot C&C strežnik…








